Webhooks
Webhook Notifications
Webhook notifications are now available for all of our Watch products, including Script Watch, Data Watch, Frame Watch and Policy Watch. It's easy to configure and can be configured per Watch product.
Enable Webhooks
On any configured Watch product, you will now see a button for Config.
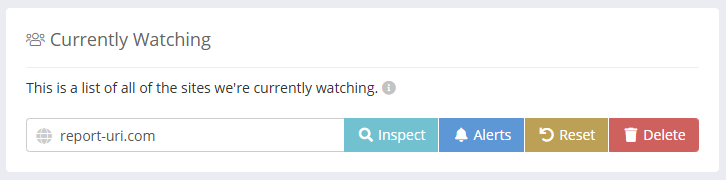
Clicking this button will open a modal with the watcher's configuration, including alert settings.
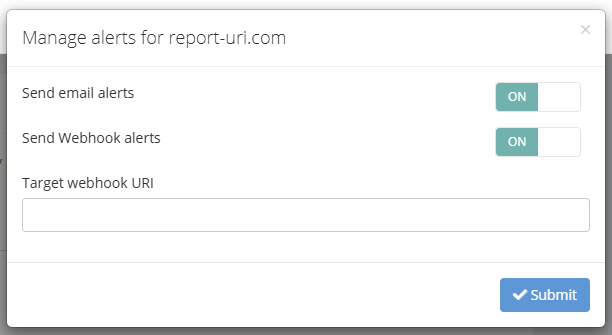
Please specify the full URI of where you would like your Webhook notifications to be sent.
Webhook Content
Watch products send two categories of webhook event: detection alerts when a new observation is recorded, and silence alerts when a Policy Watch watcher stops receiving telemetry. Both arrive as HTTP POST requests with a JSON body.
Detection alerts
When a new observation is recorded for a watcher, the JSON body can contain the following values.
| Key | Value | When |
|---|---|---|
| text | Human readable text, used for audit trail | always |
| type | watcher identifier | always |
| monitored_domain | site being watched | always |
| first_seen | ISO 8601 timestamp of first report | always |
| policy | text of policy | policy watch |
| reportOnly | boolean | policy watch |
| resourceUri | observed URI | (script-data-frame) watch |
| source | How this item was observed; csp, csp_integrity, or integrity_policy | (script-data-frame) watch |
Here is an example payload.
{
"text": "New Script Watch alert for report-uri.com : https://evil-cyber-hacker.com/malware.js",
"type": "scriptWatch",
"monitored_domain": "report-uri.com",
"first_seen": "2026-01-07T13:37:00+00:00",
"resourceUri": "https://evil-cyber-hacker.com/malware.js",
"source": "csp"
}
Silence alerts
Policy Watch can also send an alert when a watcher that was previously receiving telemetry has gone quiet for longer than a configured threshold. Silence alerts are off by default and are enabled per watcher — see the Policy Watch page for details.
| Key | Value | When |
|---|---|---|
| text | Human readable text, used for audit trail | always |
| type | always policyWatch |
always |
| monitored_domain | site being watched | always |
| last_received | ISO 8601 timestamp of last received report | always |
| silence_threshold_days | configured silence threshold in days | always |
Here is an example payload.
{
"text": "Policy Watch: No telemetry received for report-uri.com",
"type": "policyWatch",
"monitored_domain": "report-uri.com",
"last_received": "2026-04-20T08:15:00+00:00",
"silence_threshold_days": 7
}
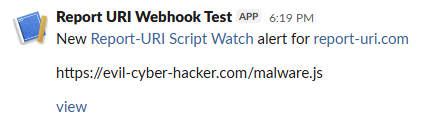
Slack Integration
When the webhook endpoint is detected as a Slack endpoint, we will format the request to produce a Slack message.
To allow us to POST messages into a Slack channel you need to provide us the Webhook URL:
- Visit https://api.slack.com/apps
- Click "Create New App", choose "From scratch", provide an "App Name" and pick your "Workspace". Then, click "Create App".
- In the new app, click "Incoming Webhooks", switch the toggle to "On" and click "Add New Webhook".
- Select your "Workspace" and then "Channel for webhook", then click "Allow".
- You can now copy the "Webhook URL" and use this in your Report URI account.
Once this is set up, any new notifications will be sent as Slack messages to your Slack channel.
Email Notifications
You can now choose to enable or disable email notifications for any configured Watch product using the Alerts section of the Config modal. Simply change the toggle for "Send email alerts" to "OFF".
Audit Trail Webhook
Available on Business and Enterprise plans, the Audit Trail webhook streams account security events to an endpoint of your choice — useful for ingesting audit logs into a SIEM or monitoring platform.
This webhook is separate from the Watch product webhooks above. It is configured once per account from Account Settings, under the Audit Trail section.
Payload
When the endpoint URL is not a Slack URL, the HTTP POST request will contain a JSON object with the following fields.
| Key | Value |
|---|---|
| type | always auditTrail — identifies the source when multiple webhooks are in use |
| account | team name (for team accounts) or email address (for personal accounts) |
| event | audit trail event identifier (e.g. apiKeyCreated) |
| text | human-readable message, prefixed with the account name |
| loggedById | internal identifier of the actor who triggered the event |
| loggedByEmail | email address of the actor, or empty string if system-triggered |
| timestamp | ISO 8601 timestamp of the event |
Example payload:
{
"type": "auditTrail",
"account": "Acme Corp",
"event": "apiKeyCreated",
"text": "[Acme Corp] API key \"main\" created by jane@example.com",
"loggedById": "abc123",
"loggedByEmail": "jane@example.com",
"timestamp": "2026-04-14T14:32:00+00:00"
}
Slack Integration
When a Slack Incoming Webhook URL is provided, the payload is formatted as Slack Block Kit instead of structured JSON. Follow the same steps in the Slack Integration section above to obtain a Webhook URL, then paste it into the Audit Trail webhook field in Account Settings.
Audit trail events will appear as structured Slack messages showing the account name, actor email, timestamp, and a summary of the event.
Events
All audit trail events are forwarded to the webhook with the exception of webhook delivery attempts, which are excluded to prevent feedback loops.
When a webhook URL is configured or removed, a corresponding audit trail event is generated (auditTrailWebhookSet / auditTrailWebhookRemoved) — so the first message your endpoint receives confirms the feed is live, and the last message it receives before deactivation is the removal notice.